What is IP Lookup
IP lookup (IP checker) is a cybersecurity and network intelligence process used to analyze a public IPv4 or IPv6 address and retrieve contextual information about its origin, infrastructure, and associated activity. It is commonly used in networking, security monitoring, fraud detection, and digital forensics.
What is an IP lookup used for?
An IP lookup is used to identify and analyze information associated with a public IP address, such as its geographic location, Internet Service Provider (ISP), Autonomous System Number (ASN), and network type. It helps determine the origin and network context of an IP address and is commonly used for cybersecurity monitoring, fraud prevention, traffic analysis, and troubleshooting network issues.
Its main purpose is to understand how an IP address is being used and what type of network it belongs to such as a residential connection, corporate network, hosting provider, VPN service, or potentially malicious infrastructure.
How does IP lookup work?
IP lookup works by querying databases that map IP address ranges to network and infrastructure records. IP lookup platforms correlate an IP address against multiple internal and external intelligence sources to build a profile of the IP address, associated network infrastructure, and observed behavioral patterns.
What data is typically returned by an IP lookup?
An IP lookup returns structured network and attribution data associated with a public IPv4 or IPv6 address. The exact fields vary by provider, but commonly include:
- IPv4 / IPv6 classification
- Autonomous System Number (ASN)
- Internet Service Provider (ISP) or hosting provider
- Organization or network owner
- Geolocation (country, region, city)
- Reverse DNS (hostname)
- Network type (residential, mobile, or datacenter)
- VPN, proxy, or Tor usage indicators
- Basic reputation or abuse indicators
- Cloud provider detection
- Historical DNS relationships
- Reputation scoring
- Blocklist / denylist presence
- Associations with spam, phishing, malware, or botnet activity
- Historical scanning behavior
- Threat actor infrastructure overlap
- First-seen and last-seen timestamps
Specialized IP Lookups (Security-Focused Analysis)
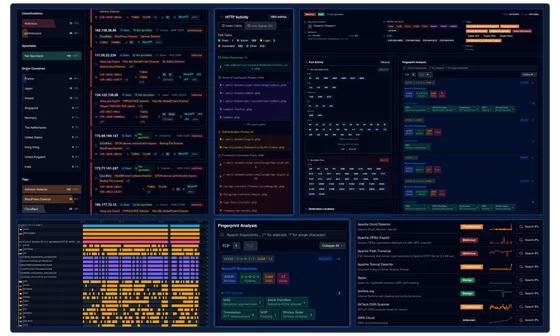
In advanced implementations, IP lookup platforms such as ELLIO IP Lookup may extend beyond basic attribution data to include security-oriented analysis of IP behavior and infrastructure context. These capabilities are designed to support threat detection, incident investigation, and the analysis of potentially malicious or exposed activity.
Such IP lookups may incorporate additional signals such as:
- Network fingerprinting: Identification of exposed services and protocol characteristics, including TLS/SSL traits and software stack indicators.
- Traffic pattern analysis: Evaluation of connection behavior, request frequency, and scanning-like activity patterns.
- Infrastructure correlation: Linking of IP addresses with related subnets, ASNs, hosting environments, and known infrastructure clusters.
- Threat intelligence correlation: Cross-referencing observed activity with known malicious indicators, historical abuse data, or coordinated attack infrastructure.
This type of analysis is typically used in security monitoring and investigative workflows where understanding behavior and context is as important as static IP attribution.
Frequently Asked Questions
Is IP lookup accurate?
IP lookup accuracy depends on the quality of the underlying database and the type of IP address being analyzed. Country-level results are generally accurate, while city-level precision can vary, especially for mobile networks, VPNs, and cloud-hosted infrastructure.
How reliable is IP reputation data in security operations?
IP reputation data is useful for prioritization but should not be treated as definitive. Reputation scores are based on historical behavior, threat intelligence feeds, and observed activity, but can sometimes produce false positives or negatives depending on data freshness and context.
Can IP lookup help identify malicious activity?
Yes, IP lookup can provide indicators of potential malicious activity, such as association with known botnets, spam operations, scanning behavior, or abuse reports. However, it is typically used as supporting context rather than definitive proof of malicious intent.
Can IP lookup detect scanning or reconnaissance activity?
Basic IP lookup typically cannot directly confirm scanning or reconnaissance activity, as it is primarily focused on static attribution data such as geolocation, ISP, and ASN information. However, advanced threat intelligence systems such as ELLIO IP Lookup can identify behavioral patterns that may be consistent with reconnaissance activity, including high-frequency probing, distributed scanning behavior, and repeated access attempts across multiple targets.
Can an IP lookup show exact location?
No, IP lookup cannot show an exact physical address. It typically provides an approximate location such as country, region, or city. The precision is limited because IP addresses are assigned to networks, not individual physical devices or users.
Who owns an IP address according to IP lookup results?
IP lookup results do not indicate personal ownership. IP addresses are allocated by regional internet registries to organizations such as ISPs, hosting providers, or enterprises. The “owner” shown in results refers to the currently assigned organization.
What is the difference between IP lookup and reverse IP lookup?
IP lookup identifies information about a specific IP address (such as location, ISP, and ASN). Reverse IP lookup starts with an IP address and attempts to identify associated domain names or hostnames hosted on that IP.
What is the difference between IP enrichment and IP lookup?
IP lookup generally refers to retrieving baseline information about an IP address, while IP enrichment combines multiple intelligence sources (threat feeds, behavioral analytics, historical activity, and infrastructure mapping) to provide deeper investigative context.
What is the role of ASN data in cybersecurity investigations?
Autonomous System Number (ASN) data helps identify which organization controls a network range. In cybersecurity, ASN analysis is used to detect infrastructure patterns, identify hosting providers frequently used for malicious activity, and correlate related IP addresses across coordinated campaigns.
![[watchdog]: Inside a Mirai variant with six-layer persistence](/_astro/Mirai%20Botnet%20with%206%20layers%20of%20persistence%20Hero_Z2qvA8g.webp)
