Stop active malicious IPs at your network perimeter.
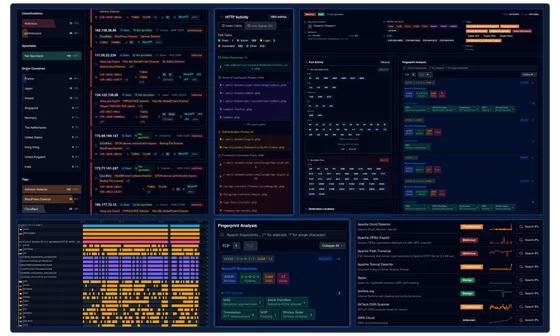
Protect your infrastructure with ELLIO’s fully configurable, high-fidelity IP blocklists, powered by advanced IP threat intelligence,network fingerprints, and a global cyber deception network.
Integrated with leading firewall vendors.
Real-time malicious IP blocking.
ELLIO IP blocklists update automatically as new malicious infrastructure is detected worldwide. Your perimeter defenses stay aligned with live attacker activity, not outdated reputation data.
High-fidelity. Low false positives.
Only verified malicious IPs are included. IPs are removed quickly once malicious behavior stops, preventing overblocking and minimizing false positives in production environments.
Protection during patch lag.
Block zero-day mass exploitation campaigns before WAF signatures are updated. ELLIO monitors active mass exploitation campaigns in real time. When attackers begin exploiting a newly disclosed CVE, the infrastructure driving the campaign is rapidly added to the blocklist.
Full control over all your ingress blocklists.
ELLIO IP Blocklists are fully configurable through ELLIO Blocklist Automation, giving security teams precise control over what is blocked and what must remain accessible across all firewalls. An automatically updated database of trusted cloud and business service infrastructure, including Google, Microsoft, AWS, and other major providers, minimizes false positives and prevents disruption to critical systems.
Take control of malicious IP traffic and unwanted scanning activity.
Take full control over malicious IP traffic and protect your network in real-time. ELLIO IP blocklists are automatically updated every 5 minutes - or as needed - ensuring your firewall always stays ahead of emerging threats.
Ultimate IP blocking with
ELLIO Threat List MAX.
Enhance your perimeter protection with a high-fidelity, dynamic, and fully configurable next-generation IP blocklist.
| ELLIO Threat List MAX | |
|---|---|
| PROTECTION | |
| Scale | 250,000 - 1,000,000 active entities |
| Coverage | |
| Active malicious IPs and known attack infrastructure | |
| Mass exploitation attempts | |
| Automated scanners, bots, and reconnaissance | |
| Brute-force, credential stuffing, and account takeovers | |
| L7 DDoS traffic sources | |
| API abuse and endpoint enumeration | |
| Cryptomining and resource hijacking probes | |
| Data source | |
| ELLIO global deception network | |
| Advanced IP Threat Intelligence | |
| 3rd party sources prone to false positives | |
| CAPABILITIES | |
| Automatic updates | |
| Update frequency | Real-time, every 5 minutes or as needed |
| Configurability | |
| False Positive control | |
| Recon IP control | |
| COMPATIBILITY | |
| Palo Alto Networks | |
| Fortinet | |
| Check Point | |
| Cisco | |
| Sophos | |
| F5 | |
| Traefik | |
| ntopng | |
| pfSense | |
| OPNSense | |
| Linux | |
| Universal | |
| PURCHASE OPTIONS | |
| Standalone IP feed with direct download | |
| Together with ELLIO Blocklist Automation Management | |
Drop noise before it reaches your SOC, SIEM, or IDS/IPS.
Reduce cloud infrastructure costs by eliminating junk traffic at the edge.

Clean up security logs for better anomaly detection and faster incident response.
Strengthen your compliance posture across PCI-DSS, NIST, CIS Controls, ISO 27001.

Drop noise before it reaches your SOC, SIEM, or IDS/IPS.
Reduce cloud infrastructure costs by eliminating junk traffic at the edge.
Clean up security logs for better anomaly detection and faster incident response.
Strengthen your compliance posture across PCI-DSS, NIST, CIS Controls, ISO 27001.
See how ELLIO works for you.
Start a free trialHow is ELLIO different from traditional IP blocking?
ELLIO delivers dynamic, context-aware IP blocking powered by real-time reconnaissance and mass exploitation intelligence from its own advanced cyber deception network. Instead of relying on static reputation or known-bad lists, ELLIO identifies attacker infrastructure based on actual behavior and intent, before it is widely classified as malicious.
It is fully configurable, allowing you to avoid false positives and protect critical business traffic. Unlike traditional blocklists, ELLIO clearly distinguishes between benign crawlers and reconnaissance linked to active campaigns, enabling security teams to act earlier, prioritize real threats, and reduce risk across the network.
How is ELLIO different from CrowdSec, Spamhaus, and other IP blocklist providers?
ELLIO builds its threat intelligence from a proprietary global cyber deception network, removing dependency on third-party data and eliminating risks like feed poisoning or stale data. It continuously correlates attacker behavior, reconnaissance patterns, and exploitation attempts, automatically updating and enforcing blocklists across firewalls in near real-time, well before signatures or static feeds can respond.
Unlike CrowdSec or Spamhaus, which provide reputation-based or community-shared lists, ELLIO delivers context-aware, high-frequency dynamic updates with automated enforcement. This approach reduces false positives, cuts operational overhead, and ensures security teams focus on real threats instead of chasing noise. ELLIO provides a proactive, precision-driven defense layer that traditional blocklists cannot match.
Does ELLIO integrate with existing firewalls?
Yes. ELLIO is integrated with major firewalls like Palo Alto Network, Check Point, Fortinet - FortiGate, Cisco, Sophos, F5, or ntopng. It’s also integrated with open source firewalls OPNsense, pfSense, and Traefik or Linux. Once you define block/allow rules, policies are automatically enforced across all your firewalls without manual syncing or vendor-specific configurations.
Can I configure ELLIO IP blocking according to my needs?
Yes. ELLIO IP Blocklists are fully configurable through ELLIO Blocklist Automation, giving security teams precise control over what is blocked and what must remain accessible across all managed firewalls. You can create custom blocklists per customer or environment, prioritize high-risk infrastructure tied to mass exploitation, and ensure trusted services - like SaaS platforms, partners, and approved scanners - are never disrupted. All policies are automatically enforced across your multi-vendor firewall environment, without manual overhead.
How does ELLIO affect false positives and SIEM noise?
ELLIO blocks only active malicious and high-risk IPs involved in active reconnaissance or mass exploitation, while ensuring critical business services, SaaS platforms, and essential bots always remain allowed.
Its fine-grained IP rules let you control exactly what gets blocked or allowed, preventing disruptions to core infrastructure. This approach drastically reduces false positives and unnecessary SIEM alerts, so security teams can focus on real threats instead of chasing noise.
How is ELLIO valuable for MSPs offering managed firewall services?
ELLIO extends managed firewall services with preemptive protection against reconnaissance and mass exploitation, going beyond what firewall vendors and static blocklists deliver. MSPs can automatically block attacker infrastructure before it turns into customer incidents, while ensuring critical business traffic is never disrupted.
Built as a multi-tenant platform, ELLIO allows MSPs to manage customizable blocklists per customer and enforce them consistently across multi-vendor firewall environments. This reduces operational overhead, lowers SIEM noise, and enables MSPs to deliver a scalable, intelligence-driven security service that clearly differentiates their offering.
![[watchdog]: Inside a Mirai variant with six-layer persistence](/_astro/Mirai%20Botnet%20with%206%20layers%20of%20persistence%20Hero_Z2qvA8g.webp)

