Eliminate threats at recon and mass exploitation stages.
Trusted worldwide as a first line of cyber resilience.






#1 Mass Exploitation and Reconnaissance Threat Intelligence.
Reduce attack risk, cost, and operational load before the attack becomes expensive, noisy, and hard to contain.
How ELLIO helps your security team
Stop attacks while they're still cheap.
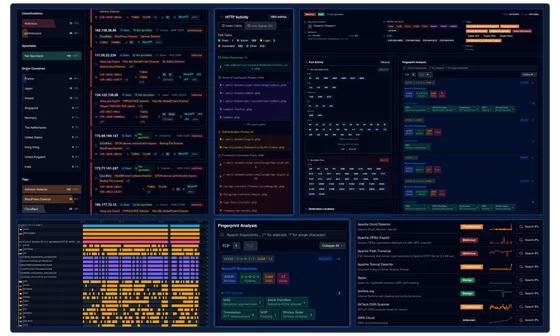
Gain actionable context on recon and exploitation as they happen. Map patterns, anomalies, and correlate connections. Manage IP rules and enforce automated blocking to prevent incidents.
Reduce incident volume and SOC workload.
Efficiently block malicious traffic and exploitation campaigns at the edge. Mask your network from unwanted scanners and reduce your attack surface.
See what's urgent and what can wait.
Add actionable context to your existing systems for faster prioritization and immediate action. Identify what requires your attention, what's noise, and what can wait.
See vulnerabilities being actively exploited.
Link active exploitation campaigns to IPs. Map CVEs. Prioritize the vulnerabilities attackers are exploiting today.
Backed by our own data.
No third-party distortion.
ELLIO operates a global deception network and honeypots, giving you direct access to core threat data with unique context, free from third-party noise and data contamination.
Latest research.
.png)
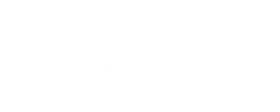
Coordinated Credential-Stuffing Campaign Targets Palo Alto GlobalProtect Portals
A coordinated credential-stuffing campaign hit GlobalProtect VPN portals with 8,575 IPs in 48 hours. Three attack waves, 78 targeted usernames, one password. Our team breaks down the timeline, infrastructure, fingerprints, and what defenders can do.
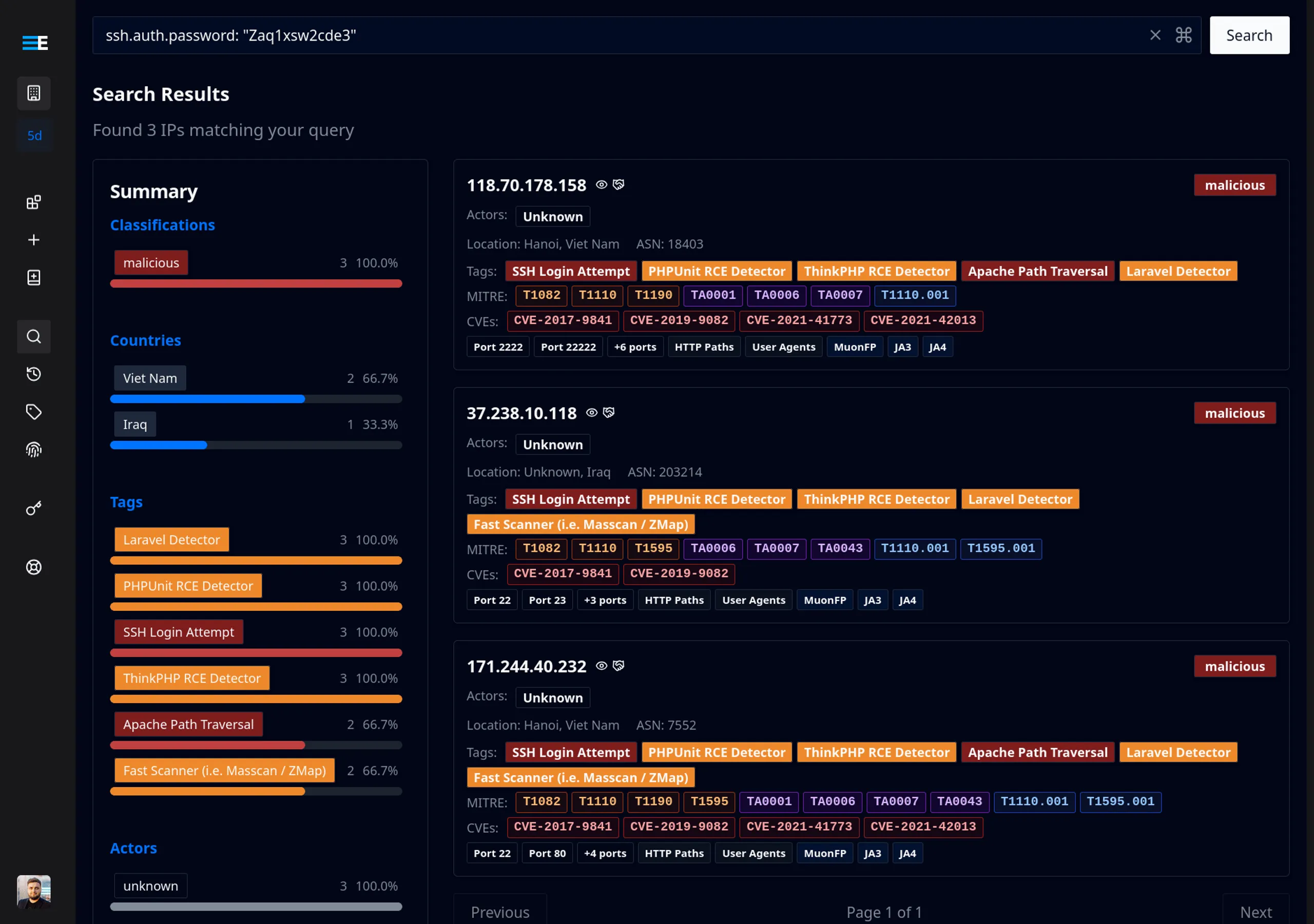
"n8n" is the new "admin."
On February 10, 2026, our deception network recorded "n8n" overtaking "admin" as the #2 most brute-forced SSH username. The campaign scaled from a handful of probing IPs to hundreds of unique sources in under a week, with attackers rapidly iterating through password variants.


New Historical IP Timeline is live
ELLIO Threat Intelligence Platform expands its capabilities with an interactive Historical IP Timeline, giving teams deep visibility into historical IP activity with flexible filtering and report-ready exports.
Disrupt kill chains early.
Reduce risk across the entire security stack.
Incident Response
SOC
Vulnerability Mng
Threat Hunting
Cloud Protection
Network Monitoring
Perimeter Defense
Attack Surface Reduction
Latest updates from us.
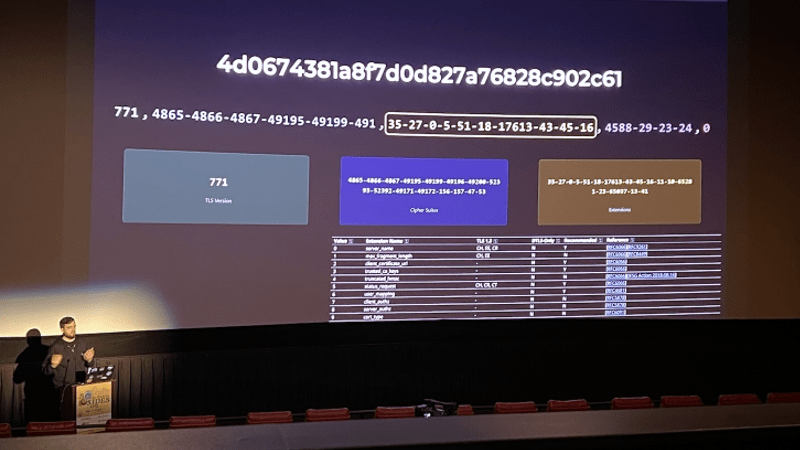
Catching up with BSides communities via network fingerprints
Throughout 2025, the ELLIO team hit the road, traveling to multiple BSides events and connecting with security practitioners who navigate noisy, complex, and often opaque network environments every day.
Black Hat 2025: ELLIO debuts new open-source recon shield
Discover the new open-source TCP Fingerprint Firewall Recon Shield, built on high-performance eBPF technology to detect and block malicious scanners using advanced MuonFP-based fingerprints. It’s designed to quickly identify scanning tools like Nmap, ZMap, and Masscan, as well as specific op...
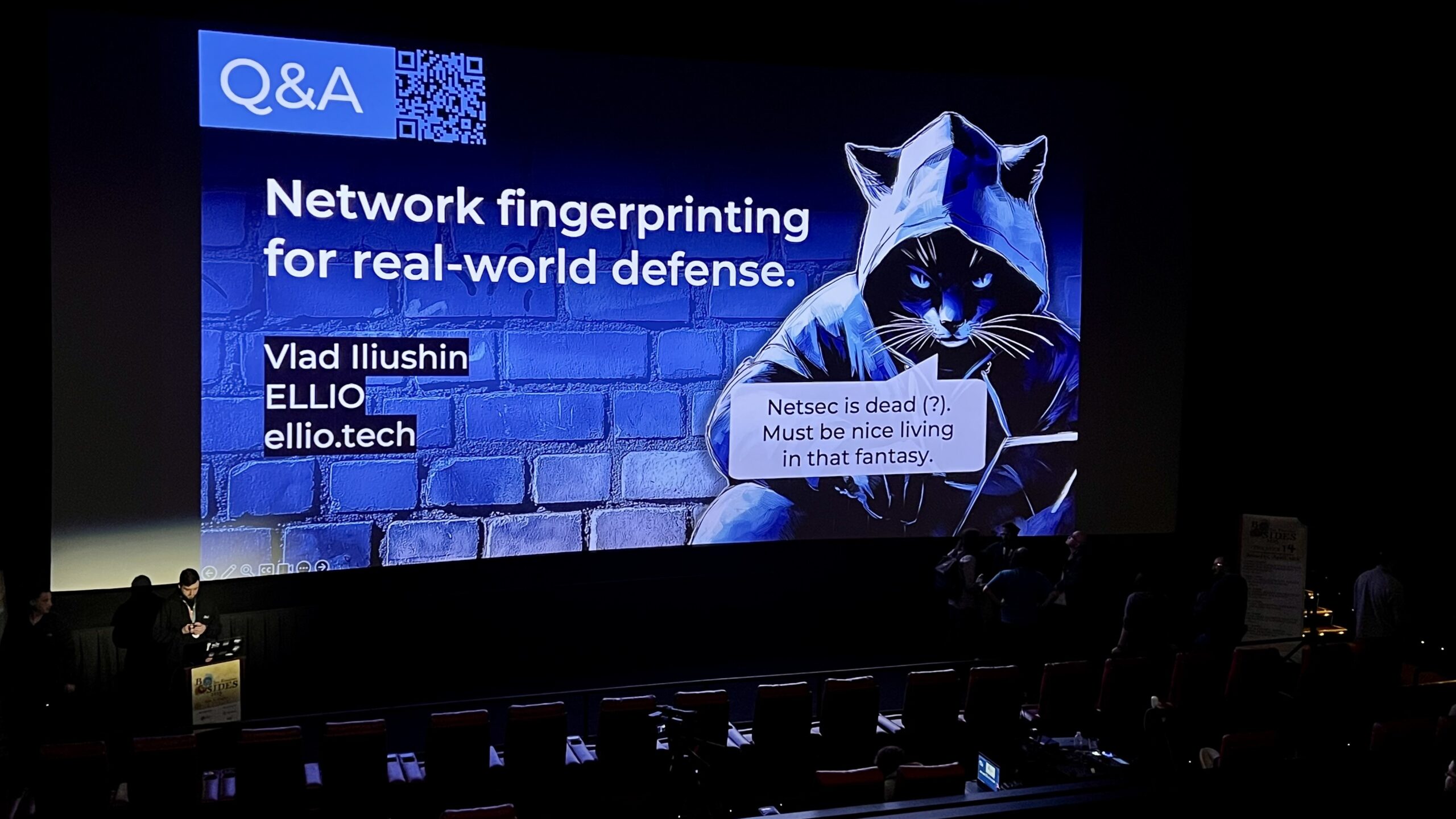
ELLIO U.S. Spring Roadshow: Unmasking recon threats and network fingerprinting.
Read how ELLIO explored the dark side of mass scanning and recon at BSides San Francisco, HackTheBay, and BSides Nashville. Discover key takeaways from the 2025 cybersecurity roadshow.
Subscribe to ELLIO updates
Get the latest ELLIO news and product updates to your inbox.
Check your inbox!
We sent a confirmation link to verify your email.
No spam. Unsubscribe anytime.